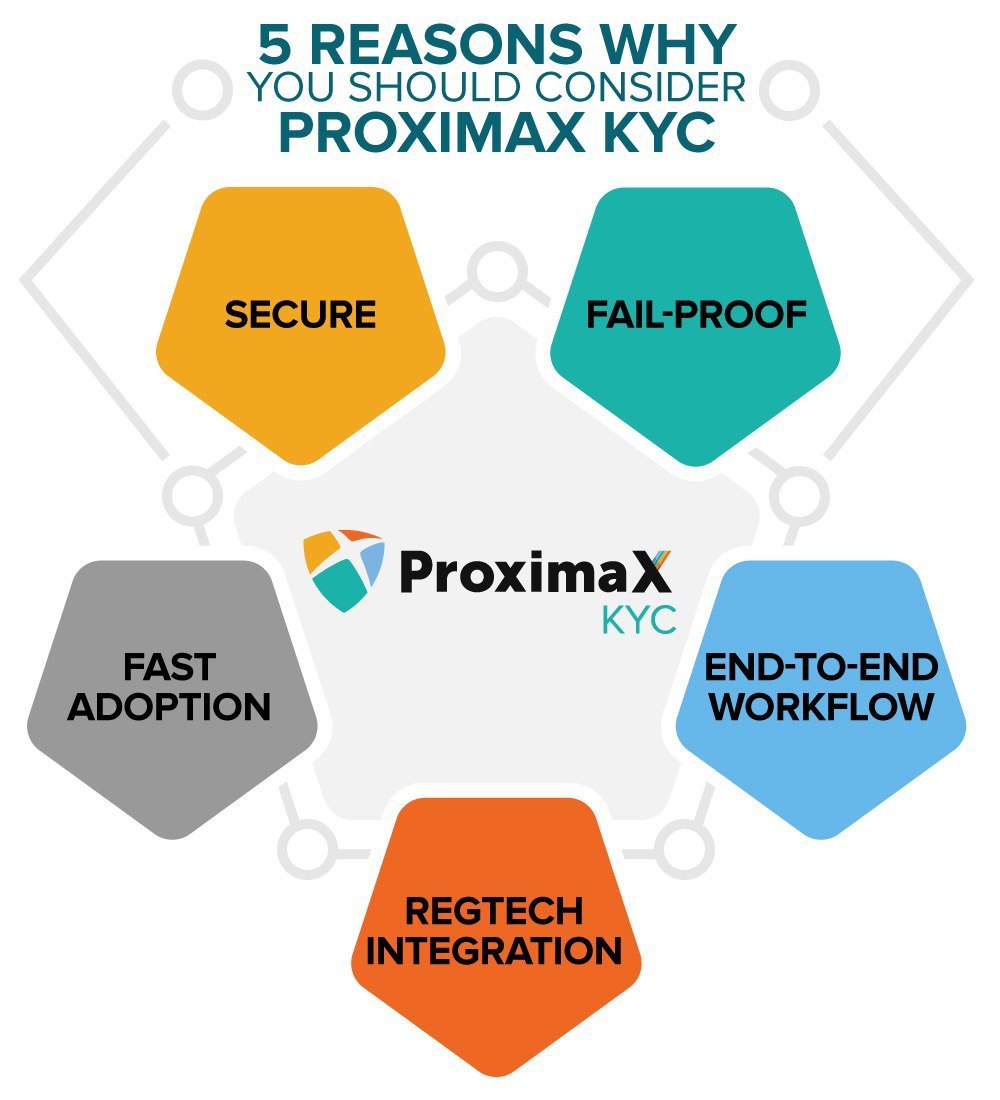
5 Reasons Why You Should Consider ProximaX KYC
The narrative of an identity management or recognition system has always inclined towards highlighting the power of authenticating data accurately, thereby minimising the risks of placing a name to a face by mistake. In the case of ProximaX KYC, our advantage against competing tech hails directly from our distinct proposition that makes it the best in its class.
In the first instance, a ProximaX product has a fundamentally well-defined architecture that positions it in a league of its own. By being a next-generation Integrated and Distributed Ledger Technology (“IaDLT”) infrastructure platform solution powered by blockchain technology means any application built on this platform will by default inherit the kind of protection commonly found in any ProximaX product or application.
As pointed out in most of our literature, ProximaX Sirius is the core technology platform that integrates several distributed and decentralised tech layers (storage, streaming, database, consensus) into one functional suite of processing power. Thanks to this multi-layer dynamism, ProximaX KYC can now comfortably boast about an inherent capability that includes the following 5 reasons for you to go from an inquisitive user to a decisive game changer.
- Secure ProximaX KYC metes out a protection strategy that combines technological wisdom and encryption marvel. Data is firstly broken into multiple pieces in a process called sharding. The broken pieces of information are then encrypted before they are stored in the nodes of the distributed file management system (“DFMS”) and the distributed database of the blockchain network. To further safeguard the information, another layer of pseudonymisation is carried out through a public key and a cryptographically unique hash for the KYC files. This smart setting of meshing the data will foil any hacking attempt, thereby keeping all John and Jane Doe’s information intact. The granting of accessibility and editable rights to only data owners also helps to secure the information even more.
- Fail Proof ProximaX Sirius is one technology that promises uptime and availability under every foreseeable. It does this by “hardwiring” codes for quick search for a replacement node so that the system doesn’t come to a halt when an earlier designated node fails to perform. Thanks to its immutability also, data is preserved until the data owner itself chooses to purge it altogether from the system. Data failure in this sense will never be an incident with ProximaX KYC.
- Fast Adoption The provisioning of SDKs (Software Development Kits) and integration through APIs (Application Programming Interface) solves the difficulty of adoption easily for any potential new user. This is because the dev team at ProximaX has worked tirelessly since inception in March 2018 to widen the door so programmers of Typescript, Javascript, Java, C#, Go, PHP, Python, Ruby etc., can all come in to integrate without much obstacle. The only killjoy (we suspect) that can come out of this swift adoption is that familiarity with the old system may find itself standing outside the doors sooner than expected. As part of our standard operating procedures also, our dedicated tech team is always out there refining the overall ProximaX Sirius platform so that applications like ProximaX KYC can continue to be at the cutting edge of technology.
- End-to-End Workflow The leadership mindset at ProximaX is thoroughly assimilated into the applications that the company builds and this is best reflected in the enterprise-like features of ProximaX KYC. So whether the procurement of ProximaX KYC is for an enterprise adoption or just a specific standalone department, it has no problems flexing its wings to plug into the different kind of workflow structures. But of course, by itself, ProximaX KYC already has an end-to-end workflow in place.
- RegTech Integration With the many RegTechs already out in the market catering to the different needs such as screening for Politically Exposed Persons (“PEPs”), sanctions, negative media, credit checks, anti-money laundering transaction monitoring, facial recognition, IP address scanning and blockchain forensics, the fully customisability of ProximaX KYC reduces the burden of would-be adopters to acquire its usage fully. In other words, no more second guessing whether compatibility is an issue or if ProximaX KYC will make the current system redundant.
Contact Us
Financial institutions, private corporations, and technical developers interested in exploring ProximaX KYC can visit KYC.ProximaX.io and contact us at KYCinfo@ProximaX.io.



